When Your Best Ideas Stop Being Yours
Intellectual property leakage can happen quietly, and by the time most organizations realize it, the damage is already done. Here is what you need to know.
At a Glance:
- Intellectual property leakage occurs when confidential information, trade secrets, or proprietary information leaves an organization without authorization
- It can result from data breaches, insider threats, human error, and even the careless use of generative AI tools
- The consequences include financial loss, legal consequences, regulatory fines, and lasting damage to an organization’s reputation
- Prevention requires data protection policies, regular audits, and limiting access to sensitive data
- IP that has already become public does not have to go to waste; platforms like TeraOpenScience offer structured ways to turn exposed or unused IP into collaborative opportunity
Intellectual property is often the most valuable thing a company or researcher owns, and losing control of it can reshape the future of a business overnight. Understanding how IP leakage happens and what to do when it does is not just a legal matter; it is a strategic one.
What Is Intellectual Property Leakage?
Intellectual property leakage refers to the unauthorized disclosure or exposure of proprietary information, trade secrets, source code, confidential data, or other protected intellectual assets. It is a form of data leakage that specifically targets the ideas, innovations, and competitive advantages that give individuals and organizations their edge.
Unlike a traditional data breach that exposes personal information or financial data, IP leakage often goes undetected for longer. There is rarely a visible sign that a trade secret has walked out the door. A competitor launches a suspiciously similar product. A patent application hits a wall because prior art has appeared. A confidential research process shows up in a rival’s workflow. These are the signals that IP leakage often announces itself with, long after the damage has been done.
IP leakage can affect:
- Startups and enterprises whose product innovations are their primary competitive advantage
- Academic researchers whose unpublished findings are leaked before formal publication
- Healthcare organizations whose proprietary treatment protocols or clinical data is exposed
- Government agencies holding sensitive content related to national or public interest research
- Individual inventors whose ideas are replicated before they can secure IP rights
How Intellectual Property Leakage Happens
IP leakage does not always involve malicious actors in hooded sweatshirts stealing files in the middle of the night. More often, it is mundane, structural, and preventable.
Human Error
One of the most common causes. An employee emails a document to the wrong recipient. A researcher shares a file through an unsecured channel. Confidential information gets uploaded to a shared drive without proper access controls. These moments of carelessness can trigger data exfiltration that is difficult to reverse.
Insider Threats
Another major vector. Not all leaks come from outside the organization. Disgruntled employees, departing staff, or contractors with unauthorized access to sensitive systems can walk out with IP either intentionally or without fully understanding what they are taking.
Generative AI Tools
AI has introduced a newer and less understood risk. When employees input proprietary information, source code, or confidential data into AI chatbots to speed up their work, that data can be ingested, stored, or used to train future models. Many organizations have not updated their security policies to address this risk, leaving a significant gap in their data protection strategy.
Cyber Criminals and External Attacks
Phishing campaigns, ransomware, and targeted intrusions are designed
to extract financial data, identifiable information, and trade secrets. Security teams that are not conducting regular audits or monitoring for unusual access patterns are particularly vulnerable.
Third-Party Exposure
When organizations share confidential data with vendors, partners, or collaborators without clear data protection agreements in place, the risk of a data leak increases substantially. A single weak link in a supply chain can expose IP that took years to develop.
The Real Cost of IP Leakage
The financial loss tied to intellectual property theft is staggering. The Commission on the Theft of American Intellectual Property has estimated that IP theft costs the U.S. economy hundreds of billions of dollars annually, with some projections placing the figure as high as $600 billion. For individual organizations, the damage compounds quickly.
Beyond direct financial loss, businesses and researchers face:
- Legal action from rights holders or competitors who claim prior ownership of exposed IP
- Regulatory fines tied to data protection regulations, particularly in industries subject to strict compliance requirements
- Competitive disadvantage when a trade secret or innovation reaches the market through a rival before the original creator can capitalize on it
- Reputational damage that erodes client trust, investor confidence, and partner relationships long after the initial leak
- Loss of patent eligibility, since public disclosure of an invention before filing can invalidate future patent claims in many jurisdictions
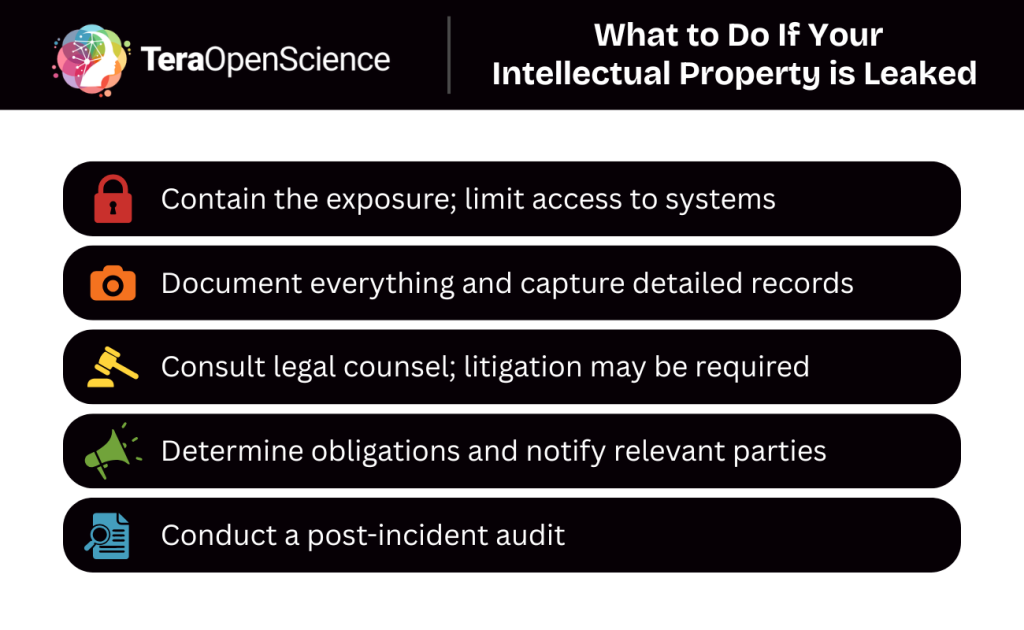
What to Do If You Are a Victim of IP Leakage
If you suspect or confirm that intellectual property leakage has occurred, the response needs to be fast, structured, and documented.
Step 1: Contain the Exposure
Limit access immediately to any systems or accounts involved. Revoke credentials, isolate compromised environments, and work with security teams to understand the scope of what was accessed or removed.
Step 2: Document Everything
Before taking any remediation steps that might overwrite logs or alter records, capture as much information as possible about what happened, when it happened, and what data was involved. This documentation will matter if legal action becomes necessary.
Step 3: Consult Legal Counsel
IP rights are complex, and the right legal response depends heavily on the type of IP involved, the jurisdiction, and the nature of the disclosure. An attorney familiar with intellectual property law can help assess whether filing for emergency injunctive relief, sending cease and desist letters, or pursuing litigation is appropriate.
Step 4: Notify Relevant Parties
Depending on the nature of the leaked information, you may have obligations to notify business partners, clients, or regulators. Data protection regulations in many regions require timely disclosure of breaches involving personal information or confidential data.
Step 5: Conduct a Post-Incident Audit
Once the immediate situation is stabilized, run a thorough review of your data security practices, access controls, and security policies. Identify the specific failure point and close it. This is also a good time to evaluate whether your current approach to limiting access to sensitive information is adequate.
Preventing IP Leakage Before It Happens
Prevention is significantly less expensive than recovery. A few best practices that organizations and researchers should have in place:
- Classify your data. Not all information carries the same level of sensitivity. Categorizing data by risk level makes it easier to apply appropriate controls.
- Limit access on a need-to-know basis. Not every employee or collaborator needs access to every system. Tighter access controls reduce the blast radius of any single leak.
- Conduct regular audits. Periodic reviews of who has access to what, and whether that access is still appropriate, catch problems before they escalate.
- Update security policies for AI tools. If your organization uses generative AI or AI chatbots, establish clear rules about what data can and cannot be entered into those systems.
- Use structured collaboration environments. When sharing IP with external partners or collaborators, use platforms with built-in data protection, NDA support, and access controls rather than informal channels.
What Happens to IP That Is Already Out There
Sometimes the leak has already happened. The trade secret is exposed. The unpublished research is circulating. The source code is public. At that point, the question shifts from how to protect it to how to make the best of the situation.
For researchers and organizations whose IP has entered the public domain, one option is to embrace open science frameworks that let you maintain attribution, build credibility, and drive collaboration even without exclusive ownership. This is where platforms like TeraOpenScience offer something genuinely useful.
TeraOpenScience is built for exactly this kind of scenario. Researchers, students, and corporate R&D teams can bring ideas, whether freshly published, already public, or deliberately open-sourced, into a structured collaborative environment where real-world R&D projects take shape. The platform includes NDA-protected workspaces for IP that still requires confidentiality, as well as open Creative Commons licensed spaces for research that is ready to be shared and built upon.
Rather than letting exposed or abandoned IP sit unused, TeraOpenScience connects it with the multidisciplinary talent needed to turn it into something actionable. A company that loses a trade secret to a data breach is not necessarily out of options. With the right platform and the right collaborators, that knowledge can still generate value.

Protect What You Can, and Build With What Remains
Intellectual property leakage is one of the more disruptive events a researcher or organization can face. The path forward requires both defensive action and a willingness to think creatively about what comes next.
If you are dealing with IP that has already entered the public sphere, or if you are sitting on research and innovation that deserves a wider audience, TeraOpenScience is the platform where that work can find new life. Join a global network of researchers, students, and industry leaders working on real R&D projects in a structured, secure, and collaborative environment. Sign up now and put your ideas to work.